We have recently released a new version of Wallarm Node.
After your next update window, you will see some new features your DevOps team is certain to like.
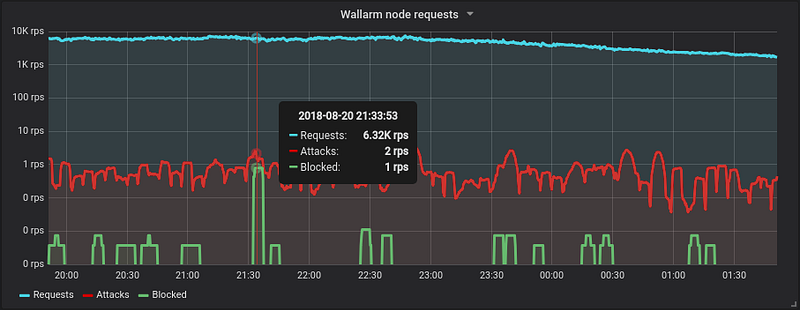
Firstly, your monitoring and reporting got a lot livelier. Starting with this version in addition to JSON format metrics can be exported in Prometheus compatible format. As before with Collectd, information on the number of requests, number of attacks, number of blocked attacks and a variety of error conditions is available.
The second big thing is a new and improved parser for HTML and JavaScript-encoded requests. Since Wallarm does not rely on regular expressions, in-depth parsing of application requests and responses regardless of the format is critical to building our application logic model and correctly detecting false positives and false negatives. The new parser will allow us to find potentially dangerous payloads (such as RCE or path traversal) even if they are entirely encoded within js or HTML elements.
By popular request, a few months ago we have added an ability to define custom detection rules manually in addition to AI-generated rules we have already had. 2.10 release makes this mechanism easier to use.
First, we have made the rules update independently from the configuration file. This means that once the rules definition is modified in the web console, it is loaded into the node within the next 15 minutes (with the next LOM update) and does not require the node reload.
Secondly, the rule definition interface is extended to accept negative rules definition (absence of the value) in addition to previously supported positive rules as well as allowing additional request parameters.
With this release, we have also introduced an option for installing Wallarm Node as a Kubernetes ingress controller. More about this in a separate blog.
Check out the release notes for the full description, configuration instructions, deprecated features and more. A new version of Wallarm Node 3.6 has been released.




